Introduction to Privacy Tools
In today’s digital age, where personal information is constantly being collected and shared, maintaining privacy has become a paramount concern for individuals worldwide. Privacy tools serve as essential safeguards, providing users with the means to protect their sensitive data from prying eyes and potential misuse. These tools empower users to regain control over their online activities by allowing them to determine what information is shared, with whom it is shared, and how it is accessed.
Definition of Privacy Tools
Privacy tools encompass a wide range of software applications, services, and techniques designed to enhance the protection of personal information in various digital contexts. These tools aim to shield individuals from unwarranted surveillance, data breaches, identity theft, and other privacy infringements. By leveraging encryption algorithms, advanced authentication methods, and secure communication protocols, privacy tools enable users to maintain confidentiality while navigating through the vast expanse of the internet.
The Importance of Privacy in the Digital Age
In recent years, there has been an exponential growth in the collection and monetization of personal data by corporations, governments, advertisers, and malicious actors. The ramifications of this pervasive surveillance culture are profound as individuals’ privacy rights erode under constant scrutiny. In this context, safeguarding personal information becomes not just a matter of preference but also an urgent necessity for preserving autonomy and protecting against potential harm.
Overview of Different Types of Privacy Tools
Privacy tools can be broadly categorized into several types based on their functionalities: 1. Virtual Private Networks (VPNs): VPNs encrypt internet traffic and route it through remote servers to mask users’ IP addresses and provide anonymity.
2. Web Browsers with Enhanced Privacy Features: These browsers incorporate features like ad-blockers, anti-tracking mechanisms,and encrypted connections to fortify user privacy during web browsing.
3. Password Managers: Password managers generate and store complex passwords for various online accounts, reducing the risk of data breaches caused by weak passwords or password reuse.
4. Encrypted Messaging Apps: These apps employ end-to-end encryption techniques to ensure that only the intended recipients can access private conversations, shielding messages from interception or surveillance. 5. Encrypted Email Services: By encrypting email communications and attachments, these services offer secure alternatives to traditional email providers, protecting sensitive information from unauthorized access or interception.
6. Privacy Settings on Social Media Platforms: Social media platforms allow users to customize their privacy settings, exercising control over what information is shared publicly and with whom it is shared. 7. Anonymous Social Media Platforms: These platforms enable users to participate in social interactions without revealing their true identities, encouraging open discussions while preserving anonymity.
General Privacy Tools
Virtual Private Networks (VPNs)
A Virtual Private Network, or VPN, is a fundamental privacy tool that allows users to create a secure and encrypted connection over the internet. By routing your internet traffic through a remote server operated by the VPN service provider, VPNs ensure that your online activities remain private and protected from prying eyes. The functioning of VPNs involves encapsulating your data within an encrypted tunnel, preventing anyone from intercepting or accessing your sensitive information.
Additionally, VPNs mask your IP address, making it harder for websites and online services to track and trace your online activities. When it comes to the benefits of using a VPN for online privacy and security, they are numerous.
Firstly, VPNs offer robust encryption protocols that safeguard your data against hackers and malicious actors seeking to intercept sensitive information like passwords or financial details. Secondly, they provide anonymity by hiding your true IP address behind the server’s IP address.
This anonymity prevents websites from tracking your browsing habits and helps protect against targeted advertising or invasive surveillance. There are plenty of reputable VPN providers in the market today.
Popular options include ExpressVPN which offers top-notch security features like AES-256 encryption and a strict no-logs policy. Another reliable choice is NordVPN known for its vast server network across different countries, enhancing both privacy protection and bypassing geo-restrictions on streaming platforms.
Web Browsers with Enhanced Privacy Features
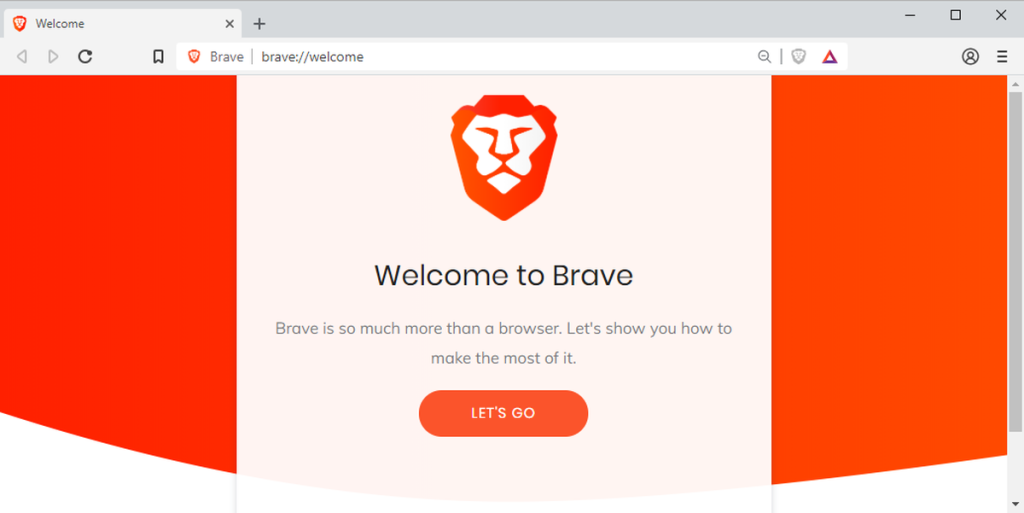
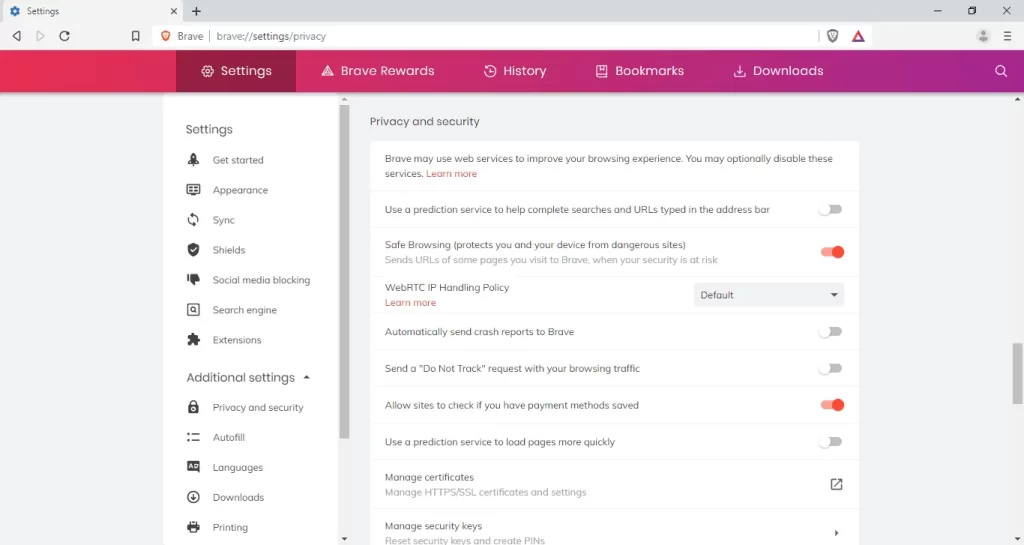
In an era where digital tracking has become ubiquitous, privacy-focused web browsers have emerged as indispensable tools for protecting one’s online privacy. Examples of such browsers include Brave and Tor which prioritize user privacy at their core.
Brave browser offers several unique features designed to enhance user privacy while browsing the web. It incorporates built-in ad-blockers that eliminate intrusive advertisements commonly used for user tracking purposes.
Moreover, Brave blocks third-party cookies by default, preventing advertisers from creating detailed profiles of users’ online activities. Additionally, Brave has a feature called “HTTPS Everywhere” which ensures that websites are loaded over encrypted connections whenever possible, safeguarding against potential data interception.
On the other hand, Tor browser is renowned for its emphasis on anonymity and avoiding censorship. It utilizes a network of volunteer-operated servers to route internet traffic through multiple layers of encryption.
This obfuscation makes it incredibly difficult for anyone to trace the origin or destination of the web traffic effectively. Furthermore, Tor incorporates anti-tracking functionalities and regularly changes user IP addresses to maintain anonymity.
When comparing privacy-focused browsers, it’s important to consider factors like ease of use, speed, compatibility with different operating systems, and availability of additional security features such as script blocking or advanced cookie management. Ultimately, selecting a web browser with enhanced privacy features can significantly enhance your online privacy and protect your personal information from being exploited by trackers and data collectors.
Password Managers
Password managers have become essential tools in managing the ever-growing number of passwords we need for various online accounts while ensuring their security. A password manager is an application that securely stores usernames and passwords in an encrypted database accessible only through a master password set by the user. The benefits of using a password manager for privacy protection are multifold.
Firstly, they enable users to generate strong and unique passwords for each online account without having to remember them all manually. This eliminates the temptation to reuse weak passwords across multiple platforms—a practice that can lead to devastating consequences if one account gets compromised.
Moreover, password managers ensure that your login credentials remain secure by encrypting them both at rest (when stored) and in transit (when synchronized across devices). They also provide features like autofill which automatically populate login forms while browsing websites or using applications securely.
When it comes to popular password manager applications, LastPass stands out as one of the most widely used options. It offers features like cross-platform synchronization, secure password sharing, and even a built-in password generator.
Another noteworthy option is Dashlane, known for its user-friendly interface and advanced security features such as Dark Web monitoring to alert users if their credentials are compromised. By utilizing a reliable password manager, users can conveniently and securely manage their passwords while ensuring that their online accounts remain protected from unauthorized access or data breaches.
Communication Privacy Tools
Encrypted Messaging Apps
Messaging apps have become an integral part of our lives, allowing us to stay connected with family, friends, and colleagues. However, the convenience of these apps often comes at the cost of privacy and security. This is where encrypted messaging apps step in.
Encrypted messaging apps such as Signal and WhatsApp employ end-to-end encryption to ensure that messages can only be read by the sender and recipient. End-to-end encryption means that the messages are securely encrypted on the sender’s device and can only be decrypted on the recipient’s device, making it nearly impossible for anyone else to intercept or decipher them.
With this level of security, users can have confidential conversations without worrying about prying eyes or potential data breaches. One notable example is Signal, a privacy-focused messaging app that has gained popularity in recent years due to its robust security features.
Signal not only encrypts text messages but also voice calls and video chats, ensuring all communication remains private from start to finish. It employs strong encryption protocols that have been endorsed by renowned cybersecurity experts worldwide.
Additionally, Signal does not store any user data on its servers, further enhancing privacy protection. Similarly, WhatsApp offers end-to-end encryption for its users’ conversations as well.
By default, all messages sent through WhatsApp are encrypted so that even if intercepted during transmission or stored on servers temporarily, they cannot be accessed without the intended recipient’s decryption key. The advantages of using encrypted messaging apps like Signal and WhatsApp go beyond secure communication.
These apps also prioritize user privacy by implementing features such as self-destructing messages that automatically delete after a designated time period or when viewed once. Some even offer additional security measures like biometric authentication (such as fingerprint or face recognition) to prevent unauthorized access to your private conversations.
Encrypted Email Services
While messaging apps dominate personal communication nowadays, email remains a crucial medium for professional and formal interactions. However, traditional email services often lack the necessary security measures to protect sensitive information from prying eyes. Encrypted email services, on the other hand, provide an extra layer of privacy and ensure that your emails remain confidential.
Encrypted email services work by encrypting the content of your messages, making it inaccessible to anyone without the encryption key. This means that even if someone gains unauthorized access to your email account or intercepts your messages during transmission, they won’t be able to read the encrypted content without decryption.
Several popular encrypted email service providers offer robust security features and user-friendly interfaces. ProtonMail is one such provider known for its end-to-end encryption and zero-access architecture.
This means that ProtonMail cannot access user data stored on their servers since only users hold the decryption keys. Additionally, ProtonMail provides features like self-destructing emails and two-factor authentication for added security.
Another notable provider is Tutanota which offers strong encryption protocols along with advanced spam filters to protect users’ inboxes from unwanted or malicious emails. Tutanota also ensures that all aspects of communication are encrypted, including subject lines and attachments.
By utilizing encrypted email services like ProtonMail or Tutanota, individuals can safeguard their sensitive information from potential threats such as surveillance or unauthorized access. These services prioritize privacy by design, offering peace of mind when it comes to online communication.
Social Media Privacy Tools
Privacy Settings on Social Media Platforms
One of the most crucial steps towards safeguarding personal information on social media platforms is understanding and properly configuring privacy settings. Major social media platforms like Facebook and Twitter offer a range of privacy options that allow users to control who can see their posts, photos, and personal details. Users should take the time to explore these settings thoroughly and make adjustments according to their comfort level.
This includes setting restrictions on who can view their profile, customizing visibility for specific posts, and managing what personal information is visible to others. Regularly reviewing and updating these settings ensures a strong defense against potential privacy breaches.
Tips for Protecting Personal Information on Social Media
In addition to adjusting privacy settings, there are several proactive measures individuals can take to protect their personal information on social media platforms. Firstly, it is essential to be mindful of the information shared publicly.
Avoid disclosing sensitive details like home address or phone numbers in public posts or profiles. Secondly, practice discretion when accepting friend requests or followers; ensure they are from trusted sources.
Thirdly, exercise caution while participating in quizzes or surveys that request access to personal data. Regularly review account activity logs and promptly report any suspicious behavior.
Anonymous Social Media Platforms
Introduction to Anonymous Social Media Platforms
For individuals seeking an extra layer of privacy beyond traditional social media platforms, anonymous social media platforms provide an alternative option. Whisper and Yik Yak are examples of such platforms where users can share thoughts, opinions, and experiences without revealing their true identity. These applications typically do not require users to create accounts or provide personal information upfront.
Benefits and Drawbacks of Using Anonymous Social Media
Using anonymous social media platforms offers certain advantages for those looking for enhanced privacy protection online. Users can freely express themselves without concerns about potential judgment or consequences since their identity remains hidden.
These platforms can also be useful for sharing sensitive information or discussing controversial topics. However, it is crucial to be mindful of the drawbacks associated with anonymity.
The absence of identity verification can lead to the proliferation of false information and cyberbullying. Additionally, the lack of accountability on these platforms may attract malicious individuals who engage in harmful activities.
Conclusion
In today’s digital landscape, privacy tools play a vital role in safeguarding personal information online. By adjusting privacy settings on social media platforms and being cautious about sharing sensitive data publicly, individuals can significantly reduce their vulnerability to privacy breaches. Furthermore, anonymous social media platforms offer an additional layer of protection for those seeking enhanced privacy, although they come with their own set of challenges.
By utilizing a combination of these tools and practices, users can enjoy a safer online experience while maintaining control over their personal information. With the right knowledge and proactive measures, individuals can navigate the digital world with confidence and peace of mind regarding their privacy and security.