Introduction to Secure Browsing
Definition and Importance of Secure Browsing
In today’s digital age, where the internet plays an integral role in our daily lives, secure browsing has become paramount. Secure browsing refers to the practice of using measures to protect one’s online activities, data, and privacy from potential threats and risks.
It involves employing various techniques to ensure that sensitive information transmitted over the internet remains confidential and inaccessible to unauthorized individuals or malicious entities. The importance of secure browsing cannot be overstated.
With the increasing prevalence of cyberattacks, data breaches, identity thefts, and other online crimes, it is critical to take proactive steps to safeguard our digital interactions. By embracing secure browsing practices, individuals can mitigate the risk of falling victim to hacking attempts, phishing attacks, malware infections, and other cyber threats that can not only compromise personal information but also disrupt businesses or cause financial loss.
Overview of Potential Threats and Risks Online
The online world is rife with potential threats and risks that can compromise our security and privacy. Cybercriminals employ a plethora of tactics to exploit vulnerabilities in systems or deceive unsuspecting users into revealing sensitive information.
Some common threats include:
- Phishing Attacks: where criminals impersonate legitimate entities (such as banks or e-commerce sites) through deceptive emails or websites in order to trick users into divulging personal data like login credentials.
- Malware Infections: malicious software such as viruses, worms, trojans, ransomware etc., which can enter a system through infected websites or downloads jeopardizing sensitive data, disrupting operations, or allowing unauthorized access.
- Data Interception: the interception of sensitive information (such as passwords or credit card details) during transmission due to lack of encryption, allowing attackers to eavesdrop and misuse the obtained data.
- Identity Theft: when cybercriminals gain access to personal information and assume another person’s identity for fraudulent purposes, leading to financial loss or reputational damage.
These are just a few examples of the risks individuals face while navigating the online realm. Understanding these threats and adopting secure browsing practices is essential in order to protect ourselves and our digital presence from potential harm.
Understanding EncryptionExplanation of encryption and its role in secure browsing:
Encryption plays a vital role in ensuring secure browsing by transforming plaintext data into ciphertext, making it unreadable to anyone without the proper decryption key. It provides a robust layer of protection against unauthorized access and eavesdropping during data transmission.
In the context of web browsing, encryption is applied to sensitive information such as login credentials, credit card details, and personal data exchanged between a user’s browser and a website. By encrypting this data, it becomes virtually impossible for malicious actors to intercept or decipher it, significantly reducing the risk of critical information falling into the wrong hands. Different types of encryption algorithms (e.g., AES, RSA):

The world of encryption encompasses various algorithms, each with its own strengths and applications. Two prominent examples are the Advanced Encryption Standard (AES) and Rivest-Shamir-Adleman (RSA).
AES is widely regarded as one of the most secure symmetric encryption algorithms used today. It operates on fixed-size blocks of data and supports key lengths of 128-bit, 192-bit, or 256-bit.
The strength lies in its resistance to known attacks while providing efficient performance. RSA is an asymmetric algorithm that utilizes two keys: a public key for encryption and a private key for decryption.
It relies on the mathematical complexity of factoring large prime numbers to ensure security. RSA is commonly used for securing communications during key exchange or establishing secure connections. How encryption protects data during transmission:
When engaging in secure browsing activities such as online banking or submitting sensitive information on e-commerce platforms, encryption safeguards your data throughout the entire transmission process. When initiating communication with a secure website (e.g., one using HTTPS), your browser and the web server establish an encrypted connection by performing a handshake.
During the handshake, both parties negotiate an encryption protocol and exchange cryptographic keys necessary to encrypt and decrypt the data. This process ensures that any information transmitted between your browser and the website remains confidential.
Encryption prevents eavesdroppers from intercepting or deciphering the data by transforming it into an unreadable format. Even if someone were to gain access to the encrypted data, without the corresponding decryption key, they would only see unintelligible ciphertext.
Secure Protocols for Web Browsing
Introduction to HTTPS (Hypertext Transfer Protocol Secure)
HTTPS, or Hypertext Transfer Protocol Secure, is an essential protocol for ensuring secure communication between a browser and a website. It builds upon the original HTTP protocol by adding an extra layer of encryption through the use of SSL/TLS technology.
This encryption ensures that data transmitted between the user’s browser and the website remains confidential and protected from eavesdropping or tampering by malicious actors. By adopting HTTPS, websites are able to establish a secure channel that safeguards sensitive information such as login credentials, financial transactions, and personal data.
The Role of SSL/TLS Certificates in Establishing Trust and Encryption
SSL/TLS certificates play a vital role in establishing trust and encryption in the HTTPS protocol. These digital certificates are issued by trusted Certificate Authorities (CAs) after verifying the identity of the website owner. When a user accesses an HTTPS-enabled website, their browser checks for a valid SSL/TLS certificate.
If it finds one issued by a trusted CA, it establishes an encrypted connection with the site using cryptographic algorithms. This encryption ensures that all data exchanged between the browser and website is securely encrypted and cannot be intercepted or altered by unauthorized entities.
Other Secure Protocols: SFTP, FTPS, SSH, etc.
In addition to HTTPS, there are other secure protocols that serve specific purposes within web browsing. One such example is SFTP (SSH File Transfer Protocol), which provides secure file transfer capabilities over SSH connections. SFTP ensures both authentication and encryption of data during file transfers, making it ideal for securely transferring files on remote servers.
Another protocol worth mentioning is FTPS (File Transfer Protocol Secure), which uses SSL/TLS encryption to provide security for FTP connections. FTPS allows users to securely upload or download files from a remote server, ensuring data confidentiality and integrity.
SSH (Secure Shell) is another significant protocol that enables secure access to remote systems. SSH establishes secure connections, allowing users to remotely log in to servers and execute commands securely.
It incorporates strong encryption algorithms, ensuring the confidentiality and integrity of the communicated data. Each of these protocols serves specific use cases where security is paramount, providing users with enhanced protection during various aspects of web browsing and file transfer operations.
Essential Security Measures for Web Browsers
Keeping browsers up to date with the latest versions
Regularly updating web browsers is a fundamental security measure that users should prioritize to safeguard their online activities. Software updates play a crucial role in patching vulnerabilities and addressing known security issues, ensuring that browsers have the latest defenses against emerging threats.
Developers constantly release updates that include bug fixes, performance enhancements, and strengthened security measures. By keeping browsers up to date, users can minimize the risk of exploitation by cybercriminals who often exploit outdated software as an entry point for attacks.
Importance of software updates in patching vulnerabilities
Software vulnerabilities are flaws or weaknesses within the code that could be exploited by hackers to gain unauthorized access or compromise user data. Regular software updates help address these vulnerabilities by fixing bugs and implementing more robust security measures. Cybercriminals are quick to identify and exploit these vulnerabilities; therefore, staying on top of browser updates is crucial in maintaining a secure browsing experience.
Automatic update settings for popular browsers (Chrome, Firefox, Safari)
Popular web browsers like Chrome, Firefox, and Safari offer automatic update settings, making it easier for users to ensure they are using the most recent version. These settings can typically be found within the browser’s preferences or settings menu.
Enabling automatic updates allows browsers to download and install new versions automatically without requiring manual intervention from users. This feature ensures that users always have the latest security patches installed without having to check for updates manually.
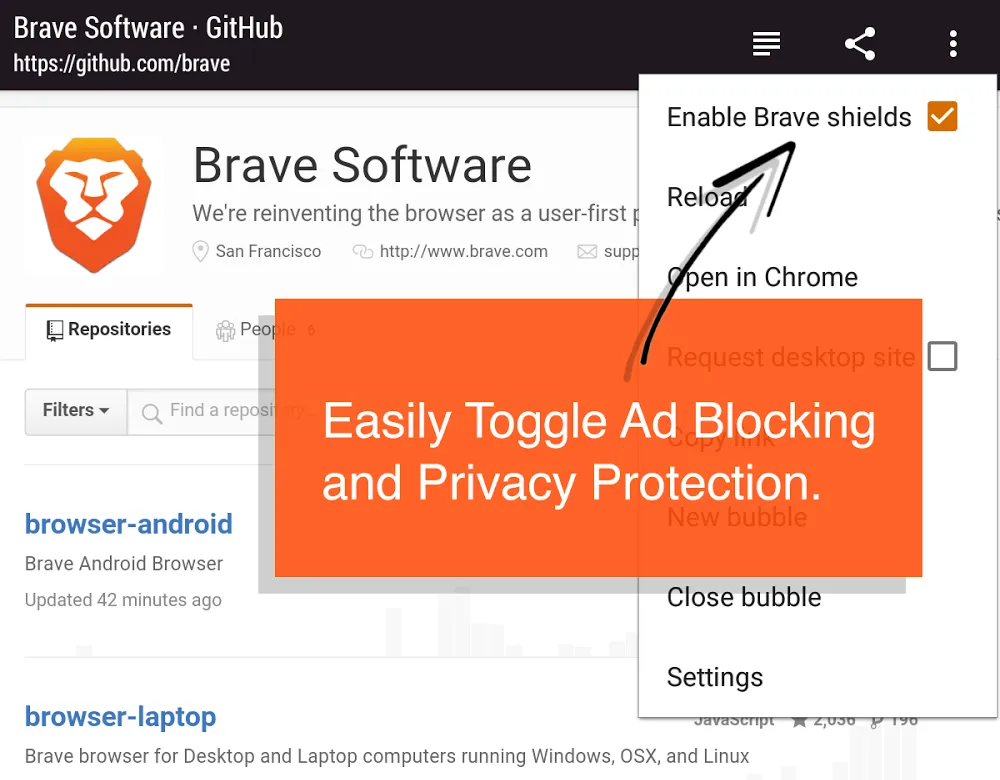
Enabling built-in security features in browsers
Modern web browsers come equipped with various built-in security features designed to mitigate risks and protect user privacy during browsing sessions. – Pop-up blockers: These tools prevent intrusive pop-up advertisements from appearing on websites, reducing distractions and minimizing the risk of inadvertently clicking on malicious pop-ups.
– Phishing protection: Browsers can detect and warn users about potentially fraudulent websites that attempt to steal sensitive information, such as login credentials or financial details. These warnings enable users to avoid falling victim to phishing attacks.
– Safe browsing modes: Many browsers offer safe browsing modes that provide an additional layer of protection against malicious websites. These modes can block access to known dangerous sites, protecting users from malware infections and other online threats.
Configuring privacy settings for enhanced security
Browsers also provide customizable privacy settings that allow users to enhance their online security and protect personal information. These settings typically include options related to cookies, website tracking, and privacy-related permissions. Users can choose whether they want to accept third-party cookies, clear browsing data regularly, or limit the information shared with websites.
Configuring these settings according to personal preferences can help reduce the exposure of sensitive data and improve overall security while browsing the web. By diligently updating web browsers and leveraging built-in security features along with proper configuration of privacy settings, users can significantly enhance their browsing security posture and minimize potential risks posed by cyber threats.
Virtual Private Networks (VPNs)
Anonymity and Security: Unlocking the Power of VPNs
In today’s digital landscape, where privacy is constantly under threat, Virtual Private Networks (VPNs) have emerged as powerful tools for ensuring secure browsing. A VPN acts as an encrypted tunnel between your device and the internet, providing a layer of protection that shields your online activities from prying eyes.
By routing your internet traffic through remote servers located in different parts of the world, VPNs conceal your IP address and make it virtually impossible for anyone to track your online presence. This anonymity serves as a safeguard against data breaches, identity theft, and targeted advertisements that compromise our privacy.
Bypassing Geo-Restrictions: Expanding Your Online Horizon
Not only do VPNs offer enhanced security, but they also provide users with the ability to bypass geo-restrictions imposed by governments or streaming platforms. With a VPN, you can choose a server location from anywhere in the world.
This effectively masks your true location and allows you to access websites and services that may be blocked or limited in your region. Whether you desire access to region-specific content on streaming platforms or need to connect with websites censored by authoritarian regimes, using a VPN enables you to break down virtual barriers and explore the vastness of the internet without limitations.
Popular VPN Services: Navigating Your Options
The market is flooded with various VPN providers offering different features and pricing plans. It is crucial to choose a reputable service that caters to your specific needs while prioritizing security and user privacy.
Among the top-rated options available today are ExpressVPN, NordVPN, CyberGhost VPN, Surfshark, and Private Internet Access (PIA). These providers offer robust encryption protocols such as OpenVPN or IKEv2/IPSec, wide server networks spanning multiple countries, and user-friendly interfaces.
Comparing their features, customer reviews, and pricing plans will help you select the VPN service that best aligns with your requirements. By harnessing the power of VPNs, individuals can reclaim control over their online experiences.
These services not only protect our data from prying eyes but also enable us to explore the internet without restrictions or fears of compromise. As we navigate an increasingly interconnected world, utilizing a VPN has become an essential safeguard for maintaining both privacy and freedom online.
Private Browsing Modes
What private browsing entails
Private browsing, also known as incognito mode or privacy mode, is a feature available in most modern web browsers that allows users to surf the internet without leaving any traces behind. When a user enables private browsing mode, the browser adopts several measures to enhance privacy and security. Firstly, it prevents the browser from storing cookies, temporary files, and browsing history during the session.
Secondly, it disables extensions and plugins that may collect data or track user activities. Private browsing also isolates each session from the regular browser windows to ensure separation between user accounts.
How private browsing modes work
Private browsing modes work by creating a separate session within the web browser that operates independently from the regular session. When activated, the browser generates a temporary profile that doesn’t store any data related to websites visited or actions taken during that session.
This means that no history is recorded in the browsing history log, form data isn’t saved, and cookies are not stored permanently on the device. It’s important to note that while private browsing prevents local storage of information on users’ devices and provides some level of privacy against others sharing access to those devices, it does not make users anonymous online nor does it protect against tracking by internet service providers (ISPs) or websites themselves.
Limitations
Although private browsing can be an effective tool for enhancing privacy in certain scenarios, it’s essential to understand its limitations. While it prevents information from being stored locally on your device and helps maintain confidentiality when using shared computers or public networks by limiting access for subsequent users of those devices or networks, it does not provide complete anonymity.
Private browsing still allows websites you visit to collect information about your activities during that session. Additionally, ISPs can still monitor your network traffic even while using private browsing mode unless you use a virtual private network (VPN) to encrypt your connection.
Moreover, private browsing does not protect against malware or phishing attempts. It is still crucial to exercise caution while browsing and to have proper security measures, such as antivirus software and ad-blockers, in place to safeguard against potential threats.
Conclusion
In an increasingly interconnected world where privacy concerns are paramount, the availability of private browsing modes in modern web browsers is a significant step towards empowering users with more control over their online activities. While it’s important to understand the limitations of private browsing modes and not rely solely on them for complete protection, they do offer a useful layer of privacy by limiting local storage of information and preventing subsequent users from accessing personal data. By combining private browsing with other security practices like using VPNs, keeping browsers updated, and practicing good internet hygiene, individuals can take proactive measures to enhance their online privacy and enjoy a safer digital experience.