Introduction to surf anonymously
Online privacy and surfing anonymously security have become pressing concerns in today’s digital age. With the vast amount of personal information we share online and the ever-increasing sophistication of cyber threats, it has become imperative to take measures to protect our identities and ensure our online activities remain private. One crucial aspect of maintaining online privacy is by surf anonymously.
Brief Explanation of the Concept of Surfing Anonymously
Surfing anonymously refers to the practice of concealing one’s identity and online activities from prying eyes while browsing the internet. It involves using various tools and techniques to hide your IP address, encrypt your data, and prevent websites, internet service providers (ISPs), and other entities from tracking your online behavior or gaining access to your personal information.
Anonymity allows individuals to maintain their privacy by preventing unauthorized monitoring, hacking attempts, targeted advertisements, or even government surveillance. By adopting anonymous browsing practices, users can regain control over their digital footprint and safeguard themselves against potential risks associated with unrestricted access to personal data.
Importance of Online Privacy and Security in Today’s Digital Age
In this technologically advanced era, where virtually every aspect of our lives is intertwined with the internet, ensuring online privacy has immense significance. Our identities are often linked to our digital presence through social media profiles, email accounts, financial transactions, and more. Consequently, potential vulnerabilities in cybersecurity can expose us to various risks such as identity thefts or fraudulent activities.
Moreover, data breaches have become alarmingly common occurrences that compromise millions of individuals’ sensitive information each year. These incidents underscore the urgency for individuals to prioritize their online security actively.
By understanding the importance of protecting privacy in an interconnected world dominated by technological advancements, we can realize that surfing anonymously serves as a shield against those who seek to exploit vulnerabilities for malicious purposes. It offers not only a sense of control over one’s online presence but also peace of mind knowing that personal information remains secure and confidential.
Differentiating between Anonymity and Privacy
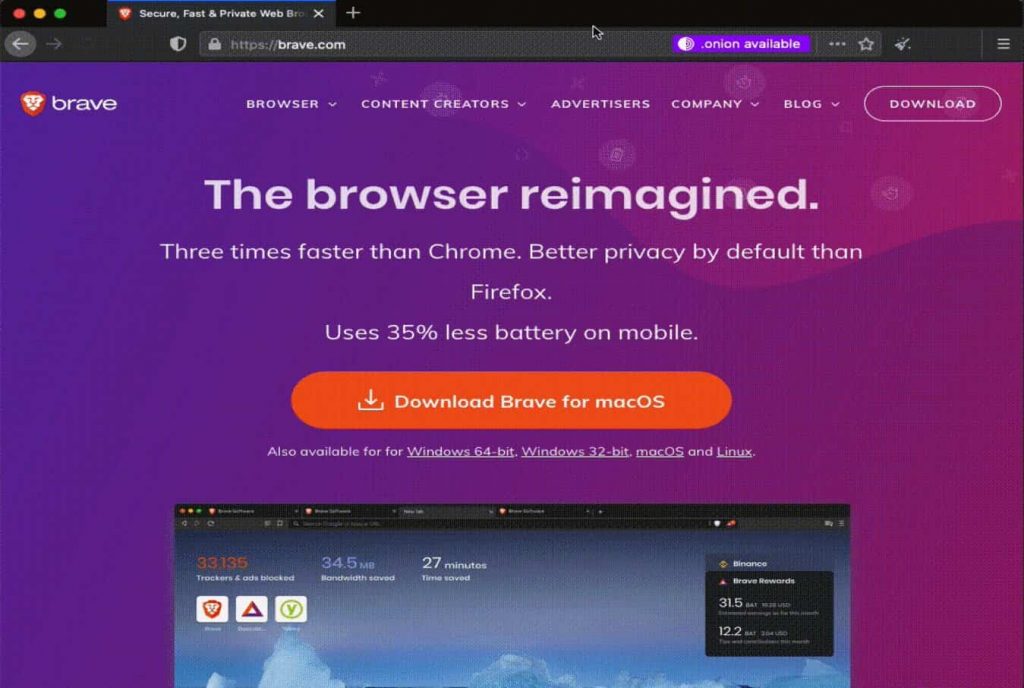
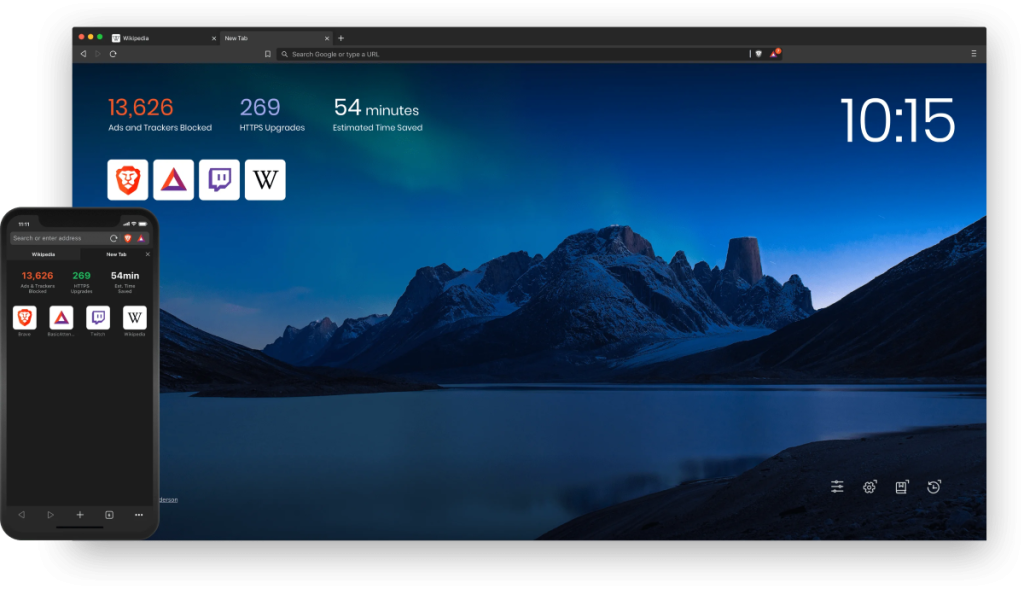
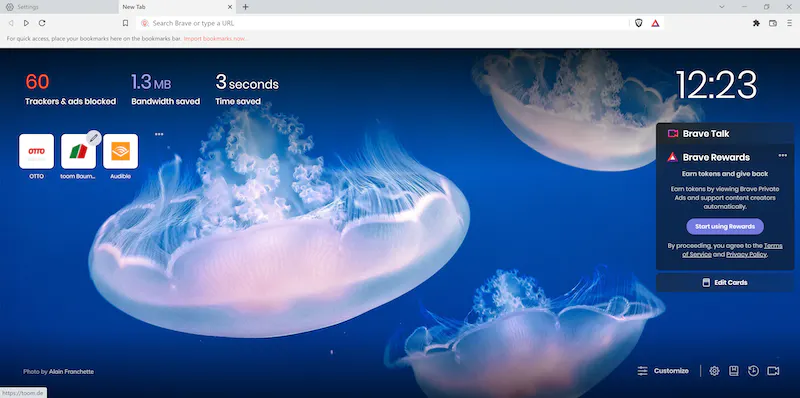
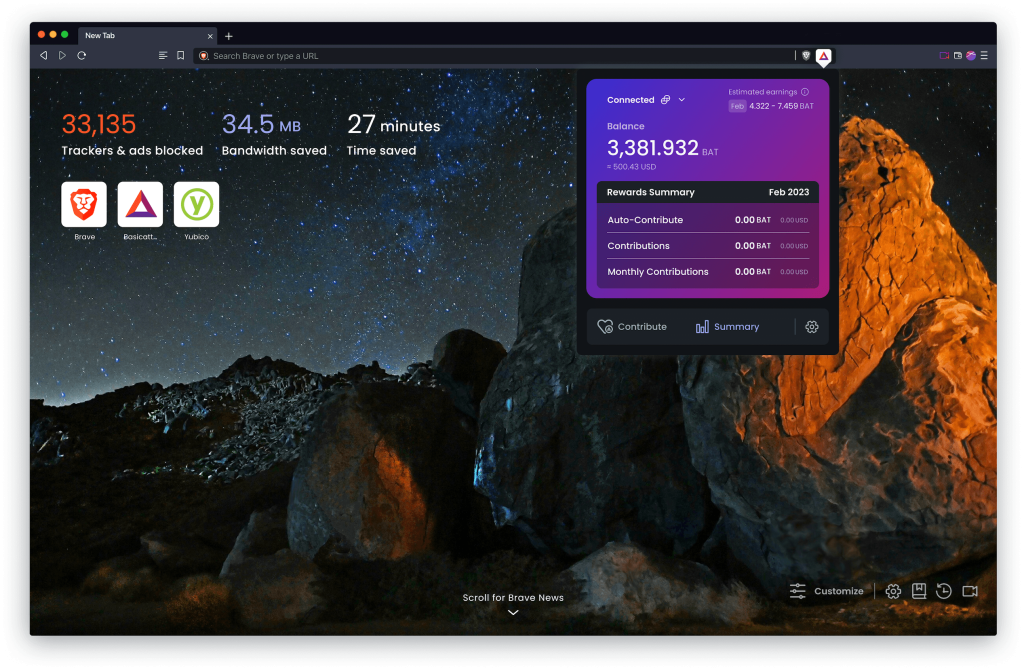
When it comes to online activities, it is crucial to understand the distinction between anonymity and privacy. While the terms are often used interchangeably, they have distinct meanings. Privacy refers to the ability to control access to one’s personal information, ensuring that it remains confidential and protected from unauthorized access. Take control of your privacy and surf anonymously with the advanced features of Brave Browser.
On the other hand, anonymity goes a step further by concealing one’s identity altogether, making it difficult for anyone to trace their online actions back to them. Anonymity focuses on hiding not only personal information but also the user’s true identity.
Exploring the Various Levels of Anonymity Online
The levels of anonymity available on the internet can vary significantly depending on various factors and technologies employed. At a basic level, users can achieve partial anonymity by using regular web browsers without any additional security measures. However, this level of anonymity still exposes certain identifying information such as IP addresses.
Moving up the ladder, more advanced techniques like using Virtual Private Networks (VPNs), Tor networks, or proxy servers provide higher levels of anonymity by encrypting internet traffic and rerouting it through multiple secure channels or intermediaries. Within these broader methods, there are even finer gradations of anonymity that users can choose from based on their specific needs. Unleash the power to surf anonymously with Brave Browser, prioritizing your online privacy.
Some VPNs may retain user logs while others claim a strict no-logs policy; this affects the level of traceability and privacy offered. Similarly, different proxy servers provide varying degrees of security and encryption protocols.
It is worth noting that achieving absolute online anonymity is incredibly challenging due to ever-evolving techniques employed by government agencies or cybercriminals for surveillance purposes. Nevertheless, with a clear understanding of these distinctions and various options available for maintaining different levels of online anonymity, individuals can make informed decisions regarding their preferred degree of privacy while navigating the vast digital landscape.
Methods to Surf Anonymously
Virtual Private Networks (VPNs)
When it comes to surfing the web anonymously, Virtual Private Networks (VPNs) are considered one of the most effective tools. Brave Browser ensures that you can surf anonymously, keeping your online footprint discreet. A VPN establishes a secure and encrypted connection between your device and the internet by routing your internet traffic through a remote server operated by the VPN provider.
This process effectively masks your IP address, making it difficult for anyone to trace your online activities back to you. By encrypting your data, VPNs also ensure that even if intercepted, your information remains unreadable and protected. Safeguard your personal information as you surf anonymously using Brave Browser’s secure features.
However, it’s important to acknowledge that while VPNs can enhance anonymity significantly, they are not foolproof. Some limitations include potential slowdowns in internet speed due to the rerouting process and reliance on the trustworthiness of the VPN provider in terms of privacy policies.
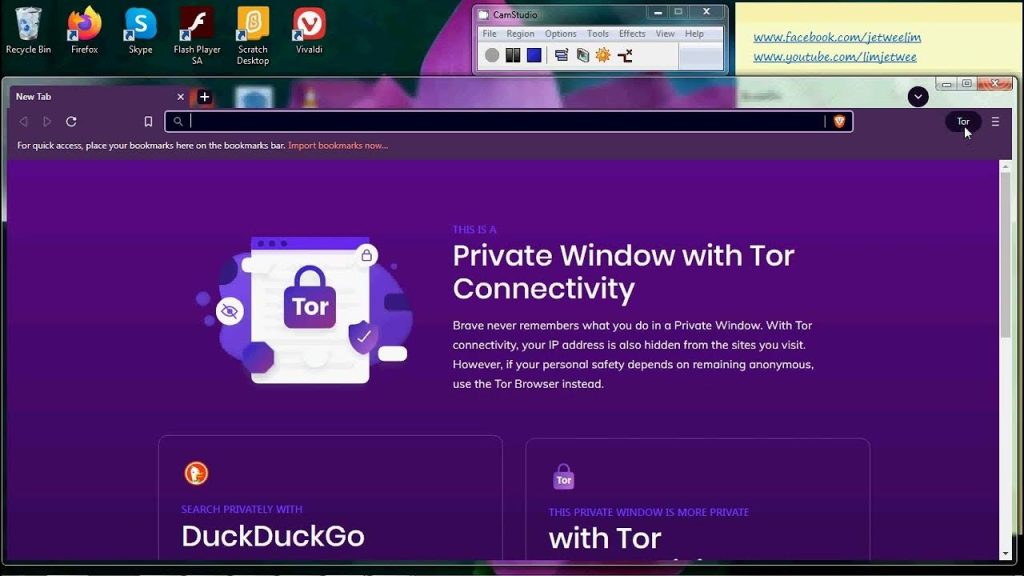
Tor Network
The Tor network offers another powerful method for anonymous web browsing. Tor stands for “The Onion Router,” highlighting its use of onion routing technology to achieve anonymity. By bouncing user data through a series of volunteer-operated servers called nodes or relays, Tor conceals users’ IP addresses and makes their online activity harder to track or trace.
This is achieved through multiple layers of encryption applied at each relay point, peeling away one layer at a time until reaching its final destination – hence the analogy of an onion. The decentralized nature of Tor makes it challenging for authorities or surveillance entities to identify and monitor users effectively. Experience the peace of mind that comes with Brave Browser’s ability to let you surf anonymously.
Proxy Servers
Proxy servers act as intermediaries between users’ devices and the internet by forwarding requests on their behalf. In anonymous surfing, proxy servers play a crucial role in masking one’s IP address as they substitute it with their own. There are various types of proxy servers available including HTTP (Hypertext Transfer Protocol), HTTPS (HTTP Secure), and SOCKS (Socket Secure).
HTTP proxies are primarily used for web browsing, while HTTPS proxies offer additional encryption for enhanced security. SOCKS proxies, on the other hand, can handle various types of internet traffic beyond just browsing.
While proxy servers provide an added layer of anonymity, it’s important to note that they can still be vulnerable to certain risks such as limited encryption and potential logging of user data by the proxy server itself. By utilizing Virtual Private Networks (VPNs), Tor network, and proxy servers, individuals seeking anonymity online have a range of options at their disposal.
Each method varies in terms of technical implementation and effectiveness but can significantly enhance privacy while surfing the web. However, it’s crucial to understand their limitations and make informed choices based on individual needs and circumstances to ensure optimal online security.
Enhancing Anonymity: Advanced Techniques
Encryption Tools: Safeguarding Your Online Identity
In the realm of online anonymity, encryption emerges as a powerful shield against prying eyes and potential data breaches. Encryption is the process of encoding messages or information in a way that only authorized parties can decipher it. It plays a crucial role in maintaining anonymity by ensuring that sensitive data, such as login credentials and personal details, remain indecipherable to anyone attempting to intercept them.
Two notable encryption tools widely used for this purpose are PGP (Pretty Good Privacy) and GnuPG. PGP, developed by Phil Zimmerman in 1991, offers end-to-end email encryption using public-key cryptography.
GnuPG, an open-source alternative to PGP, provides similar functionality but with increased flexibility and customization options. By employing these robust encryption tools, individuals can fortify their online identities and protect their information from prying eyes.
Anti-Fingerprinting Techniques: Eluding Digital Footprints
In the ever-evolving landscape of online privacy, anti-fingerprinting techniques have emerged as a means to counteract browser fingerprinting – a method employed by websites to track users based on unique characteristics of their browsers and devices. Browser fingerprinting collects various data points such as device settings, installed fonts, screen resolution, plugins/extensions, and more to create a unique identifier for each user.
However, there are strategies individuals can employ to minimize browser fingerprinting effectively. One such technique involves utilizing browser extensions specifically designed to disrupt or modify data points commonly used for fingerprinting purposes.
Additionally, regularly clearing cookies and disabling or limiting JavaScript functionality can also help reduce traceability across different websites. By adopting these anti-fingerprinting techniques proactively, users can elude digital footprints left behind while traversing the vast expanse of the internet.

These advanced techniques, encryption tools, and anti-fingerprinting methods provide individuals with the means to bolster their online anonymity. By understanding the role of encryption and employing tools like PGP or GnuPG, users can safeguard their sensitive information and communications from unauthorized access.
Furthermore, adopting anti-fingerprinting techniques allows individuals to minimize their digital footprints, making it harder for websites and third-party trackers to trace their online activities. Empowered with these advanced techniques, users can navigate the digital realm with confidence and maintain a greater level of privacy and anonymity.
Risks and Challenges
A. Potential risks associated with surfing anonymouslySurfing anonymously may provide numerous benefits, but it is important to acknowledge the potential risks that come with it. One of the main concerns is the false sense of security that some individuals may develop while using anonymity tools. While these tools can offer a certain level of protection, they are not foolproof and can still be vulnerable to skilled hackers or government surveillance agencies. Additionally, relying solely on anonymity measures can lead to complacency in taking other necessary security precautions, such as regularly updating software or using strong passwords. Users also face the risk of encountering malicious websites or downloading compromised files unknowingly, as their anonymous browsing may make them more susceptible to online scams and phishing attacks.
B. Legal implications and considerationsSurfing anonymously raises complex legal considerations that users must be aware of. The legality of using anonymity tools varies from country to country, with some nations placing restrictions on their usage due to concerns about criminal activities facilitated through anonymous networks. Therefore, it is crucial for individuals to understand the legal landscape in their respective jurisdictions before engaging in anonymous surfing. In some cases, even without engaging in illegal activities themselves, users might unknowingly access or share illegal content while utilizing certain anonymity networks like Tor. This could potentially lead to serious legal consequences if caught by law enforcement authorities who monitor such networks. It is vital for users to educate themselves about their rights and responsibilities concerning online privacy laws and stay informed about any changes or developments in legislation that might affect their use of anonymous browsing tools.
The Dark Web: Unveiling the hidden layers beyond regular internet access
The Dark Web, a mysterious realm concealed within the depths of the internet, serves as an enigmatic space distinct from the surface web we commonly navigate. It consists of websites and platforms that are intentionally hidden and accessed through specialized software like Tor.
The allure of the Dark Web lies in its anonymity, making it an attractive haven for various activities, both legal and illicit. While it is essential to acknowledge that not all content on the Dark Web is illegal or harmful, it does harbor a significant portion that can pose serious threats to individuals and societies.
Its obscurity fosters an environment where illegal trade, cybercrime, and underground communities flourish. However, researchers also utilize this covert network to gather intelligence on criminal activities or to study elements of our digital world that may otherwise remain concealed.
Cryptocurrencies: Their role in anonymous transactions
Cryptocurrencies have emerged as a groundbreaking financial innovation with profound implications for online anonymity. Unlike traditional forms of payment which rely on central authorities such as banks or governments, cryptocurrencies operate on decentralized networks using cryptographic principles.
This decentralized nature allows users to conduct transactions without revealing their true identities explicitly. While not all cryptocurrencies offer complete anonymity (some are more transparent than others), certain privacy-focused coins like Monero or Zcash prioritize concealing transaction details and user identities through advanced cryptographic techniques.
The use of these cryptocurrencies enables individuals to engage in anonymous transactions across borders securely. However, it’s crucial to note that while cryptocurrency technology provides privacy benefits, its association with illicit activities has led regulators worldwide to implement measures to monitor and regulate their usage effectively.
Conclusion
Recapitulation on the Importance of Surfing Anonymously
Surfing anonymously is not merely a luxury; it has become a necessity in today’s digital landscape. As we navigate the vast expanse of the internet, we expose ourselves to potential risks and threats to our privacy and security.
By embracing the concept of anonymity, we regain control over our online presence, safeguarding our personal information from prying eyes. Anonymity empowers us to protect our identities, maintain confidentiality, and preserve our digital rights.
Encouragement to Explore Different
In this article, we have explored various techniques and tools that enable anonymous browsing. However, this is just the tip of the iceberg. Enjoy the freedom to surf anonymously, shielding your identity from prying eyes.
The world of online anonymity is ever-evolving and offers countless avenues for exploration. With Brave Browser, you can surf anonymously, ensuring your online activities remain private. We encourage you to delve deeper into this fascinating realm by researching emerging technologies such as decentralized networks or exploring lesser-known methods like mixnets or decentralized VPNs.
By expanding your knowledge and adopting anonymous surfing practices, you can actively contribute to a more private and secure internet ecosystem while enjoying the freedom to express yourself without fear or inhibition. Remember that with every step you take towards safeguarding your online presence, you are making a difference in shaping a safer digital future for yourself and others. Brave’s commitment to privacy enables users to surf anonymously and confidently explore the web.
As you embark on this journey towards anonymity, embrace it as an opportunity for self-discovery and empowerment. Take charge of your online identity and privacy; let your virtual presence be an extension of who you truly are without compromise or fear.